Welcome to our latest cybersecurity roundup. This week, we explore critical lessons from NERC’s GridEx VII exercise, the surge in Chinese-manufactured devices in US networks, increased OT attacks by Russia’s Sandworm group, a data breach disclosure by Dell, a gift card fraud warning from the FBI, and how solar storms impacted Midwest corn planting. We’ve compiled the latest headlines to keep you informed on pressing cybersecurity developments.
1. Lessons from NERC’s GridEx exercise
A report from NERC and the E-ISAC looks at lessons learned from the GridEx VII exercise, a simulated targeting of North America’s electric grid with cyber and physical attacks. The exercise, which was conducted over two days in November 2023, involved participants from the electric sector and the government, and was followed by an in-person meeting between industry executives and government leaders from the United States and Canada. Recommendations from the report include increasing resilience for communications systems essential for operating the grid, preparing for recovery from complex and prolonged power outages, and increased coordination efforts between non-federal government partners and electric utilities. (NERC)
2. Chinese-manufactured devices in US networks see a 41% YoY increase
A report from Forescout found that the number of Chinese-manufactured devices in US networks has increased 41% year-over-year, despite official bans by the US government. The report says, “Critical infrastructure organizations are among those that use the highest numbers of such devices and some of these industries more than doubled the number of Chinese-manufactured devices in their networks in one year. One vertical of interest is the government where Hikvision and Dahua cameras, despite being banned, remain connected to networks. Other devices, including Yealink VoIP phones, are also present in the thousands.” The researchers note that vulnerable IP cameras often serve as initial access points to sensitive networks, and China-linked APTs have been known to exploit these devices in the past. (Forescout)
3. More OT attacks tied to Sandworm
Mandiant has published a report on the recent activities of Sandworm, a threat actor attributed to Russia’s GRU. Mandiant now tracks the group as “APT44,” and notes that “no other Russian government-backed cyber group has played a more central role in shaping and supporting Russia’s military campaign.” The threat actor has a much broader focus than the war in Ukraine, however, and the researchers are tracking “operations from the group that are global in scope in key political, military, and economic hotspots for Russia.”
Mandiant’s report ties APT44 to several hacktivist groups that have claimed responsibility for attacks against OT systems in the United States and the European Union, including three water utilities in Texas, a wastewater treatment plant in Poland, and a hydroelectric dam in France. These attacks don’t seem to have had any serious effects, but the researchers note that “[c]ontinued advancements and in-the-wild use of the group’s disruptive and destructive capabilities has likely lowered the barrier of entry for other state and non-state actors to replicate and develop their own cyber attack programs.” Sandworm has been responsible for several damaging attacks in the past, including the 2017 NotPetya attack and the disruptions of Ukraine’s energy grid in 2015 and 2016. (Mandiant)
4. Dell discloses data breach
Dell has disclosed a breach involving customer names and home addresses, as well as “Dell hardware and order information, including service tag, item description, date of order, and related warranty information,” TechCrunch reports. The company didn’t provide information on how many customers were affected or how the data was breached. TechCrunch notes that a user posted on a dark web forum last month claiming to be selling 49 million customer records from Dell, including “information of systems purchased from Dell between 2017 and 2024.” (Techcrunch)
5. F5 Networks warns of new Big-IP vulnerabilities
The vulnerabilities, numbered CVE-2024-26026 and CVE-2024-21793, exist in the BIG-IP Next Central Manager (NCM), a single-pane-of-glass management and orchestration solution provided by F5. Discovered by a researcher at Eclypsium, the vulnerabilities can lead to device takeover via SQL injection and OData injection respectively. F5 suggests “restricting the management access to the impacted products to only trusted users and devices over a secure network.” (Security Affairs)
6. Gift card fraud ring targets retailers’ employees
A warning from the FBI regarding Storm-0539, a financially motivated hacking group that targets the mobile devices of retail department staff using a phishing kit that enables them to bypass multi-factor authentication. After stealing the login credentials of gift card department personnel, the group seeks out SSH passwords and keys, which along with employee PII can be sold online. They then use compromised employee accounts to generate fraudulent gift cards. (BleepingComputer)
7. Solar storms delay the planting of corn
And finally, last Friday we noted that coming solar storms had the potential to disrupt electronics here on planet Earth, including the electrical grid and GPS satellite signals. Over the weekend, intense solar storms, the strongest since 2003, did indeed disrupt GPS systems crucial for self-driving tractors, causing some farmers in the Midwest to halt planting corn. This timing is critical as planting after May 15th can significantly reduce crop yields, according to the University of Nebraska-Lincoln. Farmer Tom Schwarz noted that the precision required for his organic farming is so high that only GPS can achieve the necessary accuracy. Additionally, farmers were warned that future tending to their crops based on GPS data gathered this past weekend would likely be inaccurate. The solar storms reached a G5 severity, indicating potential major impacts on power grids and communications, although significant disruptions were avoided. We had clouds here in the Baltimore area, so no northern light show for us, but some of our colleagues from the Boston area shared pictures that were spectacular. (The Verge)
8. Black Basta ransomware targets critical infrastructure entities
The US Cybersecurity and Infrastructure Security Agency (CISA) and the FBI have released a joint advisory on the Black Basta ransomware-as-a-service operation, stating that BlackBasta affiliates have breached more than five hundred organizations since the ransomware surfaced in April 2022. The advisory notes that the threat actors “have encrypted and stolen data from at least 12 out of 16 critical infrastructure sectors, including the Healthcare and Public Health (HPH) Sector.” The agencies add, “Healthcare organizations are attractive targets for cybercrime actors due to their size, technological dependence, access to personal health information, and unique impacts from patient care disruptions.” CNN cites sources as saying a Black Basta affiliate was responsible for the attack against the Ascension healthcare network last week. (CISA, CNN)
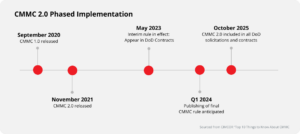
9. CMMC is coming, but concerns for small businesses persist under revamped rule
The Cybersecurity Maturity Model Certification (CMMC) is being revamped and its implementation is imminent, but significant concerns remain for small businesses. The updated rules aim to improve the security of the defense supply chain by requiring contractors to meet specific cybersecurity standards. However, small businesses face challenges such as the high costs of compliance, resource constraints, and the need for technological upgrades. These challenges could be financially burdensome, requiring investments in cybersecurity infrastructure and training for employees. Additionally, small businesses may struggle to allocate the necessary resources to meet the new requirements. (Federal News Network)
10. A malicious Python package targets macOS users
A malicious Python package named ‘requests-darwin-lite’ on PyPI, mimicking the popular ‘requests’ library, targeted macOS devices using the Sliver C2 framework, a tool for gaining access to corporate networks. Discovered by Phylum, the attack included multiple obfuscation steps such as steganography within a PNG image to covertly install Sliver. The package has since been removed from PyPI following Phylum’s report. Sliver is known for its post-exploitation capabilities and has become a preferred tool for cybercriminals due to its effectiveness in simulating adversary actions and evading detection compared to other frameworks like Cobalt Strike. This recent incident underscores the ongoing rise in cybercriminal adoption of Sliver for targeting various platforms, including macOS.
Meanwhile, Apple has extended security updates to older iPhones and iPads, addressing a zero-day vulnerability initially patched in March for newer devices. This vulnerability, found in the iOS Kernel’s RTKit, could allow attackers to bypass kernel memory protections. Although the exploiters of this flaw and the specific nature of the attacks remain undisclosed, such iOS zero-days are often used in targeted state-sponsored spyware attacks. Devices including the iPhone 8, iPhone X, and various iPad models have received the patches. Users of these devices are strongly encouraged to update immediately to safeguard against potential exploits. (Bleepingcomputer)
11. A glimpse into Africa’s internet vulnerability
Early Sunday morning, several African countries experienced a severe internet outage caused by two severed undersea cables. The incident is under investigation but is suspected to have been caused by a ship anchor. The country recently experienced two similar disruptions including back in February, when a ship’s anchor dragged through three cables in the Red Sea. Africa’s internet relies on a limited number of fragile undersea cables so when routes become unavailable, alternate pathways become jammed causing service slowdowns. Repairing damaged cables can take weeks due to requiring specialized skills and equipment and fair weather conditions. Progress toward improving Africa’s internet infrastructure challenges has been slowed by logistical and financial constraints. Experts say the problem needs to be solved through investment in diversified connectivity such as satellite internet links and vital communications infrastructure on the ground such as data centers and internet exchanges. (BBC)
12. Wichita ransomware attack resulted in data theft
The city of Wichita, Kansas has disclosed that the ransomware attack it sustained earlier this month led to the theft of personal and financial information. The city stated, “As part of our thorough review and assessment of this matter, we identified that certain files were copied from our computer network without permission between May 3 and 4, 2024. These files contained law enforcement incident and traffic information, which include names, Social Security numbers, driver’s license or state identification card numbers, and payment card information.”The city added, “We identified that this matter is related to a recently disclosed security vulnerability that affects organizations throughout the world.” SecurityWeek reports that the LockBit ransomware gang has claimed responsibility for the attack.(SecurityWeek)
13. Turla Group looks to backdoor diplomatic missions
Researchers at ESET detailed how an unnamed European Monistry of Foreign Affairs saw three of its diplomatic missions in the Middle Easter targeted by two novel backdoors. ESET said it had medium confidence that the Russian-affiliated group Turla orchestrated the attack. The LunarWeb backdoor deployed on servers, while LunarMail targeted workstations as an Outlook add-in, communicating with C2 servers over email. LunarMail spreads through a spearphishing email with malicious Word doc attachments, while LunarWeb uses a compiled ASP.NET page to decode two embedded components in the attack chain. An analysis shows both being used in targeted attacks since 2020. (The Hacker News)
Have questions? Reach out to RedSeal today to chat with one of our cybersecurity experts.